Operating System – Domain Protection mechanism Long Questions Answers
 Here in this section of Operating System Long Questions and Answers,We have listed out some of the important Long Questions with Answers on Domain Protection mechanism which will help students to answer it correctly in their University Written Exam.
Here in this section of Operating System Long Questions and Answers,We have listed out some of the important Long Questions with Answers on Domain Protection mechanism which will help students to answer it correctly in their University Written Exam.Lists of Long Descriptive type Questions that may be asked in Written Exams.
- (1) Explain Domain Protection mechanism in detail.
Question-2 Explain Domain Protection mechanism in detail.
- A computer can be viewed as a collection of processes and objects (both H/W & S/W).
- Means a computer system is collections of objects and processes and these objects and processes are needed to be protected.
- Each object has unique name by which it is referred and finite set of operations that processes are allowed to carry out on it.
- There should be some way to prohibit processes from accessing objects that they are not authorized to.
Operations that are possible depend on the object.
| Object | Operation |
| CPU | Execution |
| File | Read, Write |
| Semaphore | Up, Down |
| Tape Drives | Read, Write,Rewound |
- It is also possible to restrict processes to carry out a subset of legal operations.
- In other words we can say that process should be able to access only those resources that it currently requires to complete its task.
- This requirement is known as need to know principle.
Domain Structure
- A protection domain specifies the resources that a process may access.
- Each domain defines a set of objects and the types of operations that may be invoked on each object.
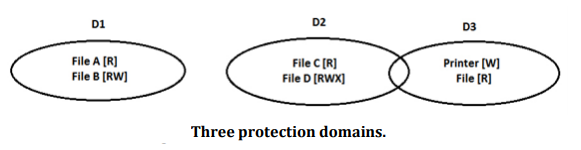
- A domain is defined as a set of < object, {access right set} > pairs. Note that some domains may be disjoint while others overlap.
- Domains need not be disjoint; they may share access rights i.e. it is possible for the same object to be in multiple domains, with different access rights each.
- An access right is the ability to execute an operation on an object.
Association between a process and a domain may be either static i.e. fixed set of resources available to a process throughout its life time or dynamic.
- In order to understand protection domain more thoroughly let us take an example of UNIX.
- In UNIX, domain of process is defined by its uid and gid. Given any (uid, gid) combination it is possible to make complete list of all objects that can be accessed and whether they can be accessed for reading, writing or executing.
- Processes with same (uid, gid) combination will have exactly same set of objects.
- One more example is that each process in UNIX has 2 halves.
- a) Kernel part
- b) User part.
- When a process does a system call, it switches from user part to kernel part.
- The kernel part has access to a different set of objects from the user part. Thus a system call causes a domain switch.